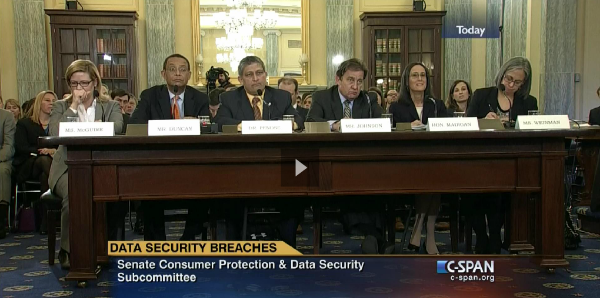
A couple weeks ago, we covered the initial hearing held by the House Subcommittee on Commerce, Manufacturing, and Trade entitled “What are the Elements of Sound Data Breach Legislation?” The Senate is pursuing a similar path and plan to propose their own version of data breach notification legislation, which started with a hearing on February 5th initiated by the Senate Subcommittee on Consumer Protection, Product Safety, Insurance, and Data Security.
Chairman Jerry Moran started the hearing by noting that "these high-profile breaches are the most severe of what has become a common occurrence in our digital society." The Verizon Data Breach Investigations Report found 1,367 confirmed breaches took place in 2013 alone - which is nearly four a day.
The first piece of testimony was delivered by Cheri F. McGuire, Vice President of Global Government Affairs & Cybersecurity Policy at Symantec Corporation. McGuire cited the NIST Cyber Security Framework, developed in 2014 as a good starting place, as "cybersecurity is about managing risk." The framework pushes five core cybersecurity functions - Identify, Protect, Detect, Respond and Recover. She did acknowledge that even the best security won't stop a determined hacker, so encrypting your sensitive data is of utmost importance.
McGuire did endorse the concept of a national standard for data breach notification, built on three principles:
1. Data security legislation applying equally to all. McGuire noted the importance of including all businesses and organizations that collect, maintain or sell personal information, whether for or non-profit, private or government entity.
2. Legislation should include pre-breach security measures. It's not fair to consumers to spend time drawing up legislation around breach notification if you're not going to make an effort to minimize the likelihood of a breach to begin with.
3. The threshold for the need for notification should be determined by the use of encryption. McGuire stressed the need to minimize "false positives," or sending notices to individuals whose stolen data was rendered useless due to encryption.
Next, the subcommittee heard from Mallory B. Duncan, General Counsel and Senior Vice President of the National Retail Federation. One of the first issues he brought up echoed the sentiments of McGuire, in that we should not be complacent in looking at developing legislation around what happens after a breach occurs. It's equally, if not more important to be looking at why these breaches are occuring in the first place, how the criminals at fault are benefitting, and how we can find ways to reduce the breaches, as well as the payoff for the hackers.
Duncan quickly took aim at the payment card industry, blaming many of the recent breaches on "an easily-forged signature" that makes the cards "particularly attractive to criminals and the cards themselves vulnerable to fraudulent misuse." He continued on, by noting that "the safety of Americans' data is only as secure as the weakest link in the chain of entities that share that data."
All of these statements were a lead-up to his request that federal legislation be comprehensive and apply to everyone who handles sensitive personal information. He cited a typical purchase process, in which personal information is passed from merchant, to a processor, through a card company, and from the cardholder bank to the acquiring bank, and that only one of those parties - the merchant - has an obligation to notify affected customers, should a breach take place. Duncan insisted that a national breach notification law would not work unless all parties had "skin in the game."
Next up was Dr. Ravi Pendse, Chief Information Officer at Brown University. Pendse brought up a point many before have belabored - which is how difficult it is to abide by 47 different state data breach notification laws. Brown University has students from 49 states and is impacted by every single one of these uniquely written pieces of legislation. Attempting to keep abreast of the differences of each of these laws is a task in and of itself, but is nearly impossible for any small, innovative organization to get a handle on.
Pendse's recommendation for a national data breach notification law included the following:
1. Closely define the rules and actions required when a breach takes place, including the method and speed of the delivery, and what sort of content should be in each notification.
2. Adjust the rules based on the size of the company and the scope of the breach. Pendse acknowledged that smaller businesses and non-profits without skills in forensics and data science may not be able to hold up a standard that is structured for much larger companies.
3. Integrate with current national legislation such as HIPAA, GLBA and HITECH.
4. Require that companies disclose what happens to customer data.
5. Define minimum security requirements for organizations that collect and store personally identifiable data.
6. Encourage the creation of and participation in industry forums. Knowledge sharing through forums such as the Financial Services Information Sharing and Analysis Center provide an opportunity to learn from fellow industry members.
7. Consider using the National Institute of Standards and Technology (NIST) to establish a baseline.
8. Provide incentives to combat data breaches by promoting programs that help educate future cybersecurity professionals.
The subcommittee then heard from Yael Weinman, Vice President for Global Privacy and General Counsel at the Information Technology Industry Council. Representing nearly 60 companies in the information and communications technology sector, the ITI is at the forefront of the fight against data breaches.
Weinman mentioned the importance of restraint in consumer notification, so as to prevent the dreaded "breach fatigue" that we so often read about. Consumers will best be served if they are only notified of the most urgent and pressing breaches, where personal identifiable information was exposed, leaving them at significant financial risk. Addressing a breach of such magnitude is a serious undertaking and should only be initiated in the most severe cases.
Weinman did challenge setting a "prescribed timeframe" for notifications, calling it counterproductive to remedying the breach and cooperating with law enforcement. Providing thorough and accurate information to consumers should be more important than providing quick, incomplete information, said Weinman.
Last, Weinman asked the subcommittee to avoid putting through legislation that allows for "private right of action," or the ability for consumers to pursue legal action against parties that violate the notification law. "Appropriate government enforcement for violations of data breach notification legislation is the proper remedy," he said.
Witness testimony was also delivered by Doug Johnson, Senior Vice President and Senior Advistor for Risk Management Policy at American Bankers Association. Johnson echoed many of the sentiments of the prior speakers, but in addition, advocated for re-assignment of the cost of the data breaches to be "borne by the entity that incurs the breach." The banking system suffered massive financial hits from the Target and Home Depot breaches, which have since resulted in lawsuits against the retailers to try and recoup some of the damages.
The sixth and final person to testify was Illinois Attorney General Lisa Madigan, who challenged the "breach fatigue" that Weinman spoke about prior. She noted that in her experience, "consumers may be fatigued over data breaches, but they are not asking to be less informed about them."
Madigan held over 25 roundtables on data breaches throughout Illinois and learned that when information is stolen, consumers want to know. They want to know how to protect themselves, and they want to know whether businesses are doing enough to protect their information in the first place. The only way to ensure this transparency is through laws mandating it, Madigan said.
Madigan also advocated for the type of information that is covered under this notification law to be broad, and not just financial in nature. "The recent attack on Sony was a lesson for all of us," she said. "Reputational harm can be far worse than financial harm."
Madigan also took issue with leaving time for a "harm analysis" to take place before deciding whether or not consumers should be notified.
"Imagine if a landlord learned that a renter's home was robbed and that landlord had the opportunity to decide whether the stolen items were significant enough to let the renter know about the robbery. We are considering allowing this for stolen data with a so-called 'harm analysis.' It will not lead to better data security, only fewer breach notifications."
Madigan went one step further and suggested a centralized location for consumers to go to learn about all data breaches, and is proposing a requirement in her home state of Illinois that breached companies notify her office as well when a breach occurs.
To keep up to speed with all the most recent data breach news, join Mastercard, Citi and the U.S. Department of Justice in subscribing to our weekly newsletter, Data Breach Ripples.


