When a data breach occurs, the full impact of the incident usually takes a few months to realize the potential impact. This has certainly been the case for the Equifax breach that was first discovered last summer. This week, the credit reporting agency announced that another 2.4 millions Americans were discovered to have been impacted by last year’s breach.
This is the second time the company has announced more affected consumers, bringing the estimated total impacted to roughly 147.9 million Americans. This is the largest data breach of personal information to date.
Read More
Topics:
Fraud,
Cybersecurity
Solving ATM fraud has become a 2 billion-dollar question. (The impact of ATM skimming on a global scale). Getting to the bottom of ATM fraud means having a better understanding of how fraudsters think, how quickly they act and what payment channels they are targeting most.
In a recent webinar hosted by the ABA and Rippleshot's Chief Data Scientist Randal Cox, we discussed case studies of actual fraudster behavior and explored patterns of ATM misuse that help financial institutions fully understand the scope of this problem — and why it’s getting worse. [Catch the full webinar here].
Read More
Topics:
Fraud,
Cybersecurity,
ATM
October is cybersecurity awareness month — a prime time for banks and credit unions to re-think how they are managing their card fraud detection strategies. Then again, companies should be doing this the other 11 months of the year, too.
Financial institution leaders need to be constantly thinking about how to evolve their card fraud detection management and update their cybersecurity measures - or risk making their organizations increasingly vulnerable. Today, fraud management is more than just reacting to industry alerts. Being reactive, instead of proactive, about cybersecurity, will leave an organization always playing catchup.
Read More
Topics:
Fraud,
Cybersecurity
“How confident are you in your company’s or client’s ability to respond to a cyberattack? What threats are keeping you up at night, and are you prepared to handle them if they strike?”
These are the types of questions addressed by Advisen and Experian in their recently released 2017 Cyber Risk Preparedness and Response Survey. The research includes responses from 307 risk managers, insurance brokers, and legal experts. The end result: a well-organized collection of valuable insights into the evolving cybersecurity landscape.
Read More
Topics:
Cybersecurity
While cybersecurity insurance is newer to the loss mitigation scene than, say, home or auto insurance, it's quickly becoming another must-have for major business. This need has been underscored by the highly publicized data breaches of Home Depot and Target. Article after article examining the circumstances surrounding these cyber thefts and their resolutions appeared in headlines for years after the breaches were contained.
Read More
Topics:
Cybersecurity
For the second year in a row, Verizon has taken its comprehensive Data Breach Investigations Report (DBIR) and converted key findings into a more easily accessible Data Breach Digest. Verizon's research is especially valuable due to the high volume of data the company is privy to. As one of the largest U.S. telecommunication corporations, its network infrastructure allows the company to draw on data from more than 82 countries and 67 contributors.
Read More
Topics:
Cybersecurity
Home Depot is still feeling the effects of the fallout from its 2014 data breach. As a reminder, the breach affected more than 50 million cardholders who used payment cards on its self-checkout terminals in U.S. and Canadian stores between April and September 2014. The cyber thief posed as a vendor, using the vendor's username and password to access both payment card data and customer email addresses.
Read More
Topics:
EMV,
Cybersecurity
Did you know that 64% – that’s right, a majority – of Americans have been directly affected by a data breach? Not surprisingly, those experiences have led a growing number of Americans to lose faith in the strength of the cybersecurity protocols major corporations and government agencies currently have in place. It has not, however, led many Americans to incorporate cybersecurity best practices into their own digital day-to-day.
Read More
Topics:
Cybersecurity
The Identity Theft Resource Center (ITRC) and CyberScout issued a new report stating that the number of U.S. data breaches reached an all-time high last year, totaling 1,093. This is a 40% increase from 2015 – quite a substantial increase indicating that rising concerns around cybercrime isn’t just hype, it’s a growing epidemic across not only the U.S but also across the globe.
Read More
Topics:
Data Breach Statistics,
Fraud,
Cybersecurity
Cybersecurity is clearly a hot topic of discussion as cyberattacks grow in scale and continue to impact all industries. While it is safe to say that most individuals, financial institutions, business organizations, etc., are all hyperaware of the growing online security threats, a new report from Gemalto indicates that consumers hold organizations - not themselves - chiefly accountable for protecting their personal data, and thus are primarily at fault when it comes to data breaches.
Read More
Topics:
Cybersecurity
Have you ever looked at your computer or phone in awe, and considered the possibility that it may be smarter than you? Although the philosophical debate surrounding the nature of intelligence has waged on for decades, the advent of machine learning has caused it to suddenly resurface. After all, when a computer can comb through years of company data and solve a complex problem within seconds, it is hard to not give heed to the argument that technology is smarter. Regardless of whether or not intelligence can be measured, the final answer is that neither is smarter, and both must work effectively together in order to find solutions to tomorrow's problems. Follow the Rippleshot Team as we discuss the origins of machine learning, its implications for the future, and how you can leverage its power to benefit your institution.
Read More
Topics:
Cybersecurity,
Machine Learning,
Data Analytics
Although version 3.2 of the PCI Data Security Standard (PCI DSS) was released over half a year ago, its impact will stretch much further into the future. In a way, the strategic introduction of the standard is the most noteworthy element about it. There are a few essential changes, but the projected runway provides more than enough time for organizations to brace themselves. As Payment Card Industry Security Standards Council's CTO Troy Leach stated in an interview, he believes the postponed update will give organizations the time they need to effectively implement security processes that help mitigate against cyberattacks. However, this does not mean that companies are off the hook, as today’s “most advanced” security technology can become a vulnerability to exploit for tomorrow’s cyber criminals. Follow along as the Rippleshot Team looks at The Key Highlights of PCI DSS 3.2.
Read More
Topics:
Fraud,
Cybersecurity,
PCI,
Cryptography,
Payments
It’s safe to say that 2016 has been a year of heightened turmoil for the payments and security industry. With the aftermath of EMV implementation, a sharp rise in data breaches, and unprecedented fraud losses by issuers, we know that this year has kept you busy. The good news is, we’re here to help. In order to save you time, we have compiled a list of key statistics that paint the bigger picture of the industry as a whole. Follow the Rippleshot Team as we take you through the Top 11 Stats of 2016.
Read More
Topics:
EMV,
Fraud,
Cybersecurity,
E-Commerce,
Friendly Fraud,
CFPB,
Payments
We know it’s hard to believe, but sometimes even your beloved customers have malicious intentions. According to a newly published whitepaper by Radial, the majority of eCommerce fraud originates from cyber criminals, who use compromised payment data to make unauthorized transactions, and make managing eCommerce fraud extremely challenging. Merchants are forced to constantly balance risk exposure with customer disturbances, heavily invest in fraud detection technologies, and dedicate resources to preventing fraud. However, what happens when the customer is the one committing fraud? Commonly known as “friendly fraud”, this type of first party fraud is when customers transact online, and then claim their purchase was unauthorized. Follow the Rippleshot Team as we quantify how much friendly fraud has been costing merchants (quick teaser- billions), and the steps merchants should take to avoid it.
Read More
Topics:
Compromises,
Fraud,
Cybersecurity,
E-Commerce,
Friendly Fraud
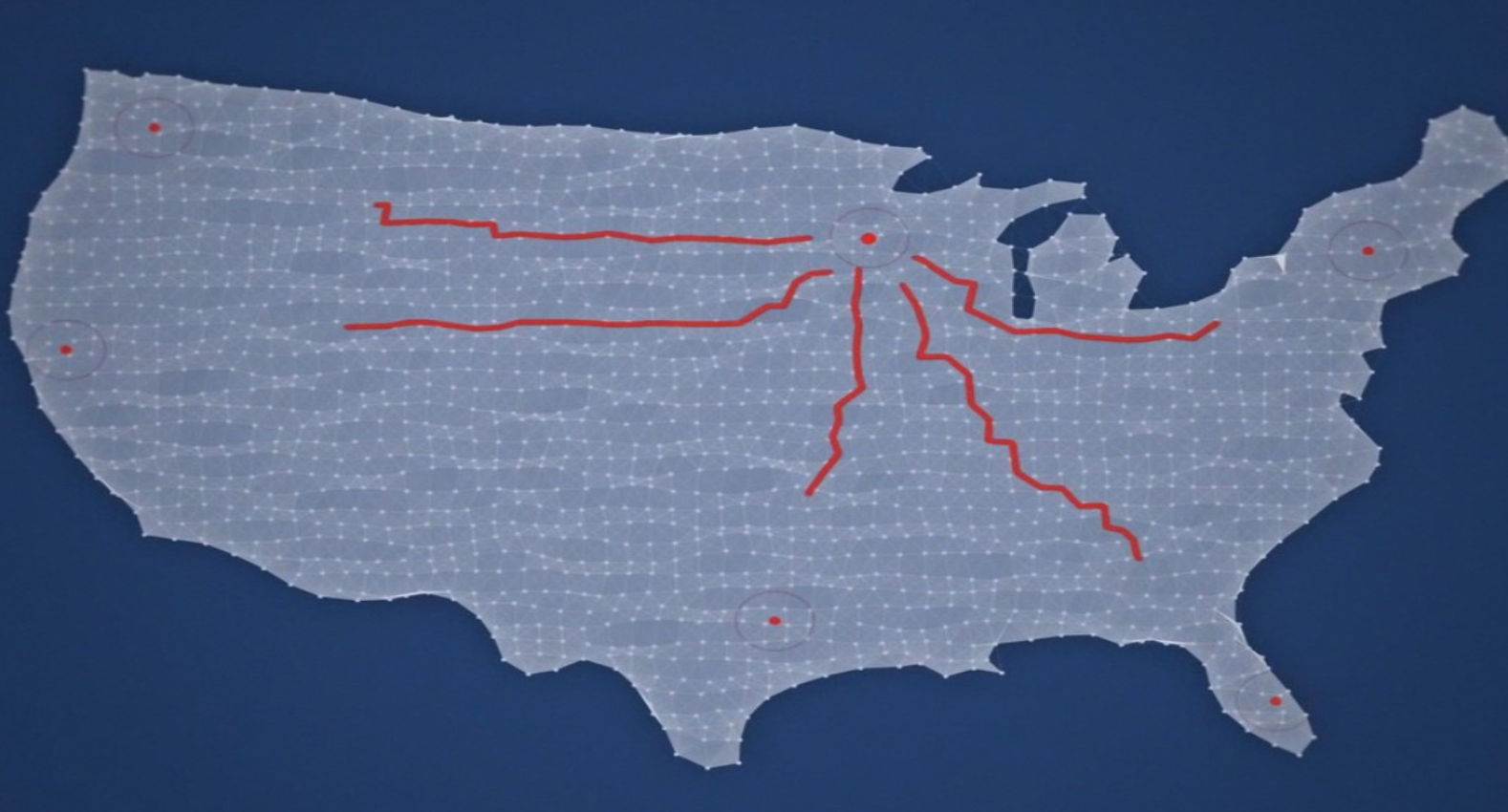
During March, the Rippleshot Team covered the top locations and trends of e-commerce fraud in a previous blog post, outlining where both the fraudsters and victims of fraud were located. Much of our focus was on warning financial institutions that EMV implementation was not the cure-all to fraud, as fraud, and its impact of customers, was not going anywhere. Some listened, while some countered that their “fraud losses were lower than ever because of EMV”. So although we don’t like to say we told you so…we told you so. Experian’s latest report, published right around the 1-year anniversary of the EMV liability shift, projects 2016 e-commerce fraud attack rates to be at least 15% higher than last year’s total. Learn the Top 10 Riskiest Zip Codes for shipping and billing fraud in our latest blog- “The Where and What of E-Commerce Fraud”.
Read More
Topics:
Fraud,
Cybersecurity,
E-Commerce